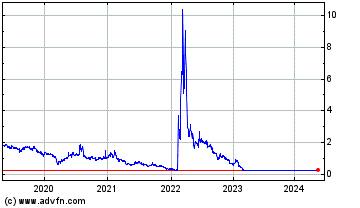
CYREN (NASDAQ:CYRN)
Historical Stock Chart
From Jul 2019 to Jul 2024